Nmap是一款針對大型網路的埠掃描工具,被廣泛應用於黑客領域做漏洞探測以及安全掃描,其主要功能有主機發現(Host Discovery)、 埠掃描(Port Scanning)、 版本偵測(Version Detection) 、操作系統偵測(Operating System Detection ...
Nmap是一款針對大型網路的埠掃描工具,被廣泛應用於黑客領域做漏洞探測以及安全掃描,其主要功能有主機發現(Host Discovery)、 埠掃描(Port Scanning)、 版本偵測(Version Detection) 、操作系統偵測(Operating System Detection),可以適用於winodws,linux,mac等操作系統。
1、yum安裝nmap
yum install nmap

nmap 命令參數:nmap -h
[root@lamp01 scripts]# nmap -h Nmap 5.51 ( http://nmap.org ) Usage: nmap [Scan Type(s)] [Options] {target specification} TARGET SPECIFICATION: Can pass hostnames, IP addresses, networks, etc. Ex: scanme.nmap.org, microsoft.com/24, 192.168.0.1; 10.0.0-255.1-254 -iL <inputfilename>: Input from list of hosts/networks -iR <num hosts>: Choose random targets --exclude <host1[,host2][,host3],...>: Exclude hosts/networks --excludefile <exclude_file>: Exclude list from file HOST DISCOVERY: -sL: List Scan - simply list targets to scan -sn: Ping Scan - disable port scan -Pn: Treat all hosts as online -- skip host discovery -PS/PA/PU/PY[portlist]: TCP SYN/ACK, UDP or SCTP discovery to given ports -PE/PP/PM: ICMP echo, timestamp, and netmask request discovery probes -PO[protocol list]: IP Protocol Ping -PR: ARP ping - does not need HW address -> IP translation -n/-R: Never do DNS resolution/Always resolve [default: sometimes] --dns-servers <serv1[,serv2],...>: Specify custom DNS servers --system-dns: Use OS's DNS resolver --traceroute: Trace hop path to each host SCAN TECHNIQUES: -sS/sT/sA/sW/sM: TCP SYN/Connect()/ACK/Window/Maimon scans -sU: UDP Scan -sN/sF/sX: TCP Null, FIN, and Xmas scans --scanflags <flags>: Customize TCP scan flags -sI <zombie host[:probeport]>: Idle scan -sY/sZ: SCTP INIT/COOKIE-ECHO scans -sO: IP protocol scan -b <FTP relay host>: FTP bounce scan PORT SPECIFICATION AND SCAN ORDER: -p <port ranges>: Only scan specified ports Ex: -p22; -p1-65535; -p U:53,111,137,T:21-25,80,139,8080,S:9 -F: Fast mode - Scan fewer ports than the default scan -r: Scan ports consecutively - don't randomize --top-ports <number>: Scan <number> most common ports --port-ratio <ratio>: Scan ports more common than <ratio> SERVICE/VERSION DETECTION: -sV: Probe open ports to determine service/version info -sR: Check what service uses opened ports using RPC scan --version-intensity <level>: Set from 0 (light) to 9 (try all probes) --version-light: Limit to most likely probes (intensity 2) --version-all: Try every single probe (intensity 9) --version-trace: Show detailed version scan activity (for debugging) SCRIPT SCAN: -sC: equivalent to --script=default --script=<Lua scripts>: <Lua scripts> is a comma separated list of directories, script-files or script-categories --script-args=<n1=v1,[n2=v2,...]>: provide arguments to scripts --script-trace: Show all data sent and received --script-updatedb: Update the script database. OS DETECTION: -O: Enable OS detection --osscan-limit: Limit OS detection to promising targets --osscan-guess: Guess OS more aggressively TIMING AND PERFORMANCE: Options which take <time> are in seconds, or append 'ms' (milliseconds), 's' (seconds), 'm' (minutes), or 'h' (hours) to the value (e.g. 30m). -T<0-5>: Set timing template (higher is faster) --min-hostgroup/max-hostgroup <size>: Parallel host scan group sizes --min-parallelism/max-parallelism <numprobes>: Probe parallelization --min-rtt-timeout/max-rtt-timeout/initial-rtt-timeout <time>: Specifies probe round trip time. --max-retries <tries>: Caps number of port scan probe retransmissions. --host-timeout <time>: Give up on target after this long --scan-delay/--max-scan-delay <time>: Adjust delay between probes --min-rate <number>: Send packets no slower than <number> per second --max-rate <number>: Send packets no faster than <number> per second FIREWALL/IDS EVASION AND SPOOFING: -f; --mtu <val>: fragment packets (optionally w/given MTU) -D <decoy1,decoy2[,ME],...>: Cloak a scan with decoys -S <IP_Address>: Spoof source address -e <iface>: Use specified interface -g/--source-port <portnum>: Use given port number --data-length <num>: Append random data to sent packets --ip-options <options>: Send packets with specified ip options --ttl <val>: Set IP time-to-live field --spoof-mac <mac address/prefix/vendor name>: Spoof your MAC address --badsum: Send packets with a bogus TCP/UDP/SCTP checksum OUTPUT: -oN/-oX/-oS/-oG <file>: Output scan in normal, XML, s|<rIpt kIddi3, and Grepable format, respectively, to the given filename. -oA <basename>: Output in the three major formats at once -v: Increase verbosity level (use -vv or more for greater effect) -d: Increase debugging level (use -dd or more for greater effect) --reason: Display the reason a port is in a particular state --open: Only show open (or possibly open) ports --packet-trace: Show all packets sent and received --iflist: Print host interfaces and routes (for debugging) --log-errors: Log errors/warnings to the normal-format output file --append-output: Append to rather than clobber specified output files --resume <filename>: Resume an aborted scan --stylesheet <path/URL>: XSL stylesheet to transform XML output to HTML --webxml: Reference stylesheet from Nmap.Org for more portable XML --no-stylesheet: Prevent associating of XSL stylesheet w/XML output MISC: -6: Enable IPv6 scanning -A: Enable OS detection, version detection, script scanning, and traceroute --datadir <dirname>: Specify custom Nmap data file location --send-eth/--send-ip: Send using raw ethernet frames or IP packets --privileged: Assume that the user is fully privileged --unprivileged: Assume the user lacks raw socket privileges -V: Print version number -h: Print this help summary page. EXAMPLES: nmap -v -A scanme.nmap.org nmap -v -sn 192.168.0.0/16 10.0.0.0/8 nmap -v -iR 10000 -Pn -p 80 SEE THE MAN PAGE (http://nmap.org/book/man.html) FOR MORE OPTIONS AND EXAMPLES
2、nmap 常用命令介紹:
掃描單個主機:
nmap 192.168.43.118
掃描單個子網主機:
nmap 192.168.43.0/24
掃描多個主機:
nmap 192.168.43.117 192.168.43.43.99
掃描一個範圍內的主機:
nmap 192.168.43.1-254
若你有一個ip地址表,將ip地址存在ip.log文件中,命令如下:
nmap -iL ip.log
若你想查看掃描的所有主機列表命令如下:
nmap -sL 192.168.43.1/24
掃描一子網主機且排除某一個ip命令:
nmap 192.168.43.1/24 -exclude 192.168.43.118
掃描一子網主機且排除某一個ip地址表命令:
nmap 192.168.43.1/24 -exclude ip.log
掃描主機路由跟蹤信息:
nmap --traceroute 192.168.43.118
掃描主機信息結果詳細輸出:
nmap -vv --traceroute 192.168.43.118
掃描某主機上指定的埠或協議,例如80,21,22
nmap -p U:53,T:80,21,22,S:9 192.168.43.118 (其中T代表TCP協議、U代表UDP協議、S代表SCTP協議)

快速掃描埠模式,掃描100個最有可能開放的埠 -v 獲取掃描的信息
nmap -F -v 192.168.43.118

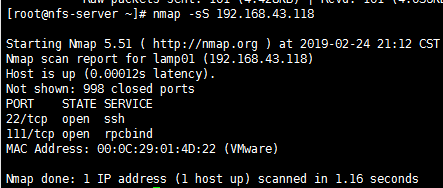
Tcp SYN Scan (sS) 隱蔽掃描
這是一個不完整的掃描方式,它被稱為半開放掃描,Nmap發送SYN包到遠程主機,但是它不會產生任何會話,在syn掃描中不需要通過完整3次的握手,因此不會在目標主機上產生任何日誌記錄,這個就是SYN掃描的優勢,但是這種掃描是需要root許可權(對於windows用戶來說,是沒有root許可權這個概念的,root許可權是linux的最高許可權,對應windows的管理員許可權)
nmap -sS 192.168.43.118
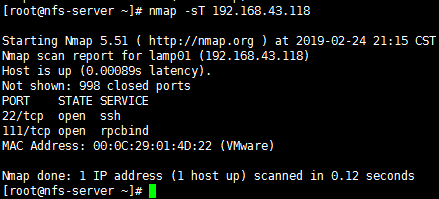
Tcp connect() scan(sT) 最常用
如果不選擇SYN掃描,TCP connect()掃描就是預設的掃描模式,不同於Tcp SYN掃描,Tcp connect()掃描需要完成三次握手,並且要求調用系統的connect(),Tcp connect()掃描技術只適用於找出TCP和UDP埠,但是這種方式掃描的速度快,準確性高,對操作者沒有許可權上的要求,但是容易被防火牆和IDS(防入侵系統)發現。
nmap -sT 192.168.43.118
UDP scan(sU)
顧名思義,這種掃描技術用來尋找目標主機打開的UDP埠,它不需要發送任何的SYN包,因為這種技術是針對UDP埠的。UDP掃描發送UDP數據包到目標主機,並等待響應,如果返回ICMP不可達的錯誤消息,說明埠是關閉的,如果得到正確的適當的回應,說明埠是開放的。
nmap -sU 192.168.43.118
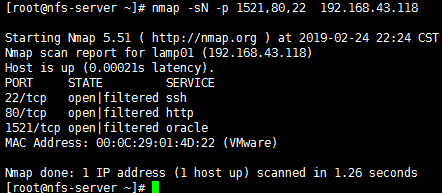
FIN scan (sF)
有時候Tcp SYN掃描不是最佳的掃描模式,因為有防火牆的存在,目標主機有時候可能有IDS和IPS系統的存在,防火牆會阻止掉SYN數據包。發送一個設置了FIN標誌的數據包並不需要完成TCP的握手,收到RST回覆說明該埠關閉,否則說明是open或filtered狀態
nmap -sF 192.168.43.118
PING Scan (sP) 掃描線上主機
PING掃描它只用於找出主機是否是存在在網路中的,它不是用來發現是否開放埠的,PING掃描需要ROOT許可權,如果用戶沒有ROOT許可權,PING掃描將會使用connect()調用。
nmap -sP 192.168.43.118
版本檢測(sV)
版本檢測是用來掃描目標主機和埠上運行的軟體的版本,它不同於其它的掃描技術,它不是用來掃描目標主機上開放的埠,不過它需要從開放的埠獲取信息來判斷軟體的版本,使用版本檢測掃描之前需要先用TCP SYN掃描開放了哪些埠。
nmap -sV 192.168.43.118
Idle scan (sL)
Idle scan是一種先進的匿名掃描技術,它不是用你真實的主機Ip發送數據包,而是使用另外一個目標網路的主機發送數據包,例如:通過目標網路中的192.168.43.118向主機192.168.43.4發送數據,來獲取192.168.1.1開放的埠。
nmap -sL 192.168.43.118 192.168.43.4
有需要其它的掃描技術,如 FTP bounce(FTP反彈), fragmentation scan(碎片掃描),IP protocol scan(IP協議掃描),以上討論的是幾種最主要的掃描方式。
Nmap的OS檢測(O)
Nmap最重要的特點之一是能夠遠程檢測操作系統,Nmap的OS檢測技術在滲透測試中用來瞭解遠程主機的操作系統是非常有用的,通過獲取的信息你可以知道已知的漏洞
nmap -O 192.168.43.17

ACK掃描:
利用ACK掃描判斷埠是否被過濾。針對ACK探測包,為被過濾的埠(無論打開或關閉)會回覆RST包
nmap -sA -T4 p1521,80 192.168.43.17
使用TCP ACK (PA)和TCP Syn (PS)掃描遠程主機
nmap -pA -T4 p1521,80 192.168.43.17
nmap -pA -T4 p1521,80 192.168.43.17
掃描前不進行Ping掃描測試:
nmap -Pn p1521,80 192.168.43.17
通過tcp空掃描以繞過防火牆檢測:
nmap -sN 192.168.43.17
列印主機介面和路由
nmap --iflist
按順序掃描埠:
nmap -r 192.168.43.118
掃描主機檢測是否有防火牆過濾:
nmap -PN -p 1521 192.168.43.17

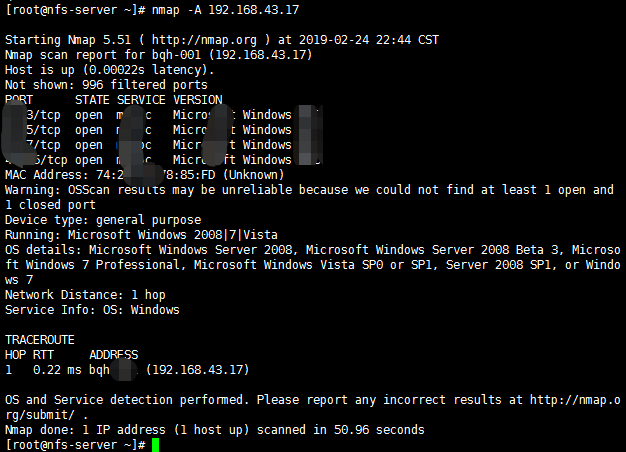
掃描操作系統信息和路由跟蹤
使用Nmap,你可以檢測遠程主機上運行的操作系統和版本。為了啟用操作系統和版本檢測,腳本掃描和路由跟蹤功能,我們可以使用NMAP的“-A“選項。
nmap -A 192.168.43.17
掃描埠時狀態介紹:
Open 埠開啟,數據有到達主機,有程式在埠上監控
Closed 埠關閉,數據有到達主機,沒有程式在埠上監控
Filtered 數據沒有到達主機,返回的結果為空,數據被防火牆或者是IDS過濾
UnFiltered 數據有到達主機,但是不能識別埠的當前狀態
Open|Filtered 埠沒有返回值,主要發生在UDP、IP、FIN、NULL和Xmas掃描中
Closed|Filtered 只發生在IP ID idle掃描
以上總結來源於網路。