預設情況下啟動docker容器都是bridge網路,橋接到docker0橋;對於docker容器來講,各個容器之間的網路上相互隔離的;相互隔離就表示在第一個容器里監聽某個埠,對於第二個容器是不可見的;對於宿主機來講,兩個容器的網路都是共用docker0橋的網路;同時在宿主機上的網路名稱空間中是可... ...
上一篇博客我們主要聊了下docker鏡像相關的說明以及怎樣基於現有鏡像製作鏡像、分發鏡像到docker倉庫中的相關測試;回顧請參考https://www.cnblogs.com/qiuhom-1874/p/12941508.html;今天我們來聊一聊docker的網路相關說明;
在使用vm虛擬機時,我們知道一個虛擬機可以有三種虛擬網路介面,第一種網路是橋接網路,第二種是NAT網路,第三種是僅主機網路;這三種虛擬網路介面後面對應的都是一個個不同的虛擬網路;我們要想讓虛擬機在那個網路中工作就把對應介面更換成那個介面即可;相對於docker來講,docker內部也有三種虛擬網路介面,它們分別是bridge,host,none這三種;bridge是docker容器預設的網路類型,啟動容器不指定網路時預設是bridge,該網路類型是橋接到宿主機的docker0橋上的,而docker0橋上一個NAT橋;host在docker里不是僅主機網路類型,它這裡的意思是共用宿主機網路,即同宿主機共用同一網路名稱空間;none表示空網路類型,在docker的網路中表現形式就是我們啟動容器指定網路類型為none,在容器內部除了lo介面就沒有別的其他網路介面,這意味著該容器網路只能自己和自己通信,有點類似vm里的僅主機網路;其實除了以上三種網路,docker也支持自定義網路;自定義網路就是可以創建網路名稱空間,docker支持的網路類型有bridge host ipvlan macvlan null overlay;
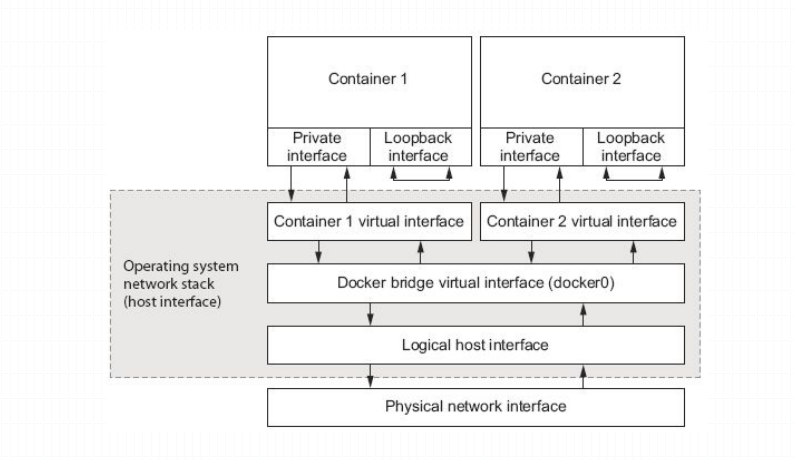
提示:以上這張圖描述了兩個容器的網路。預設情況下啟動docker容器都是bridge網路,橋接到docker0橋;對於docker容器來講,各個容器之間的網路上相互隔離的;相互隔離就表示在第一個容器里監聽某個埠,對於第二個容器是不可見的;對於宿主機來講,兩個容器的網路都是共用docker0橋的網路;同時在宿主機上的網路名稱空間中是可以看到兩個容器的虛擬介面是連接到docker0橋的;所以預設情況啟動的容器相互之間是可以基於docker0來通信;我們可以把docker0橋理解成連接兩個容器的交換機;
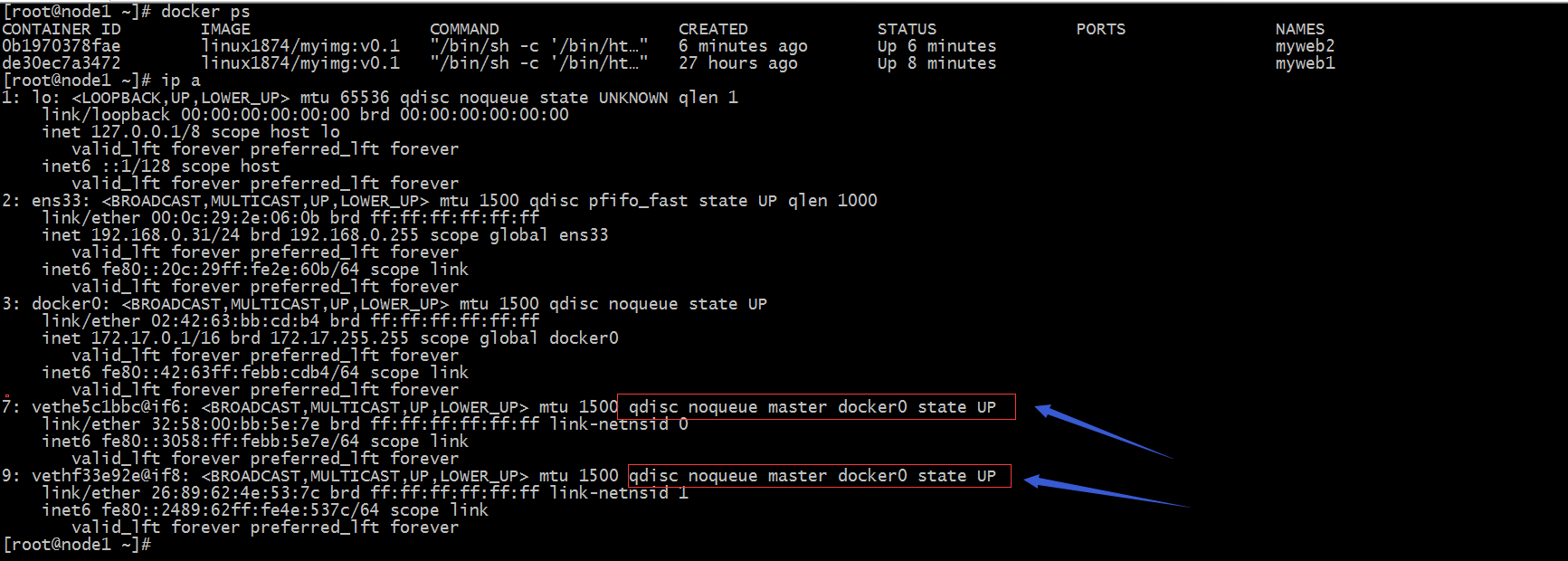
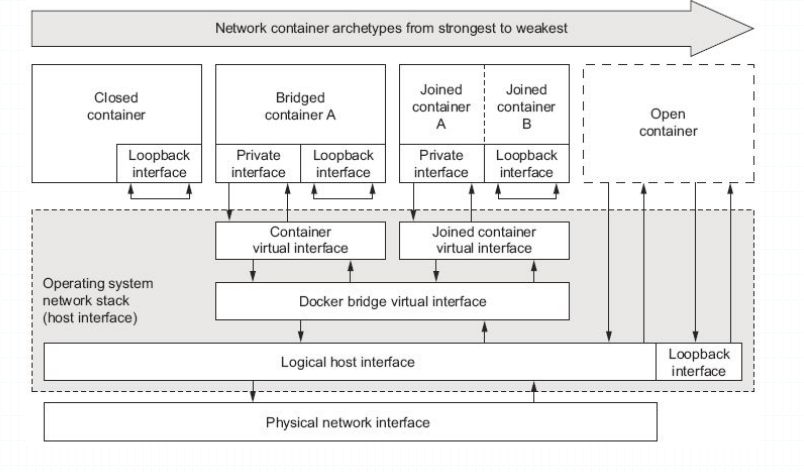
提示:可以看到宿主機上跑了兩個容器,他們的虛擬網路介面都是鏈在docker0橋的;所以這兩個容器是可以相互通信的;但是對於宿主機以外的主機,他倆是不可見;宿主機以外的主機上沒法和這兩個容器通信的,原因是docker是一個nat橋;如下所示
提示:以上規則表示源地址為172.17.0.0/16並且不從docker0橋出去的報文,在通過POSTROUTING鏈時會做地址偽裝(SNAT);從上面的信息我們就可以確定docker0橋就是一個nat橋;
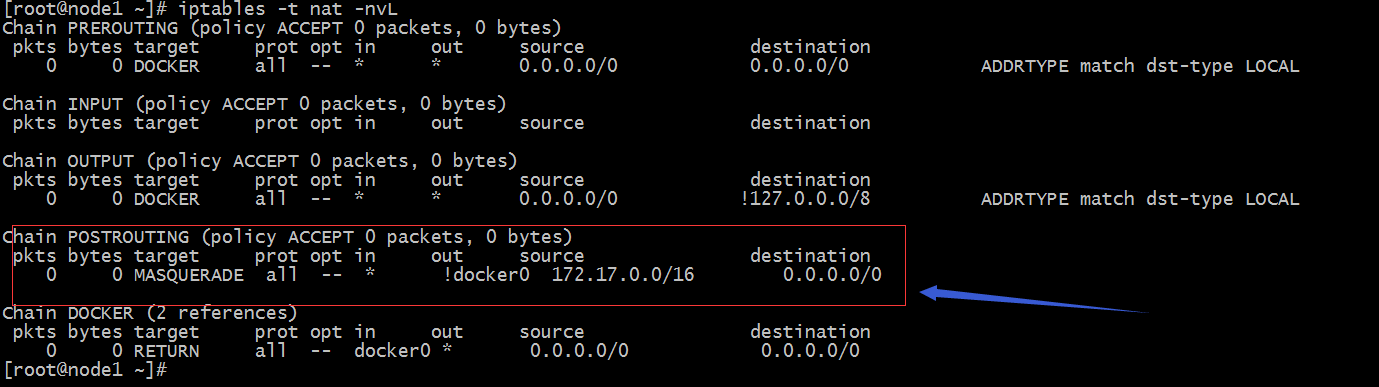
提示:以上圖片展示了docker的三種網路,closed container這個容器只有一個lo介面,和其他容器相互隔離,只能自己和自己通信;bridged container這種橋接式網路容器,通常都會有兩個介面,一個lo迴環介面,一個連接至宿主機上的docker0橋的乙太網介面;docker daemon 啟動時預設會創建一個名為docker0的網路橋,並且創建的容器為橋接式容器(就是創建的容器的網路橋接至docker0上的)用docker運行容器時我們可以使用--net或--network來指定容器的網路,預設是--net bridage;docker0橋上一個nat橋,因此,橋接式容器可以通過自己的橋介面訪問到外部網路,但是防火牆規則組織了一切從外部網路訪問橋接式容器的請求;對於open container來講其實就是共用宿主機的網路名稱空間,相當於在網路這層資源上不和宿主機隔離;joined container 我們理解為聯盟式網路容器;該容器的網路資源是鏈接到其他容器的網路資源;本質上就是多個容器共用一個網路空間;
示例:bridge網路的容器創建
[root@node1 ~]# docker ps
CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES
[root@node1 ~]# docker run --name web1 -d --net bridge linux1874/myimg:v0.1
bced86e3dcb2e8144ade7cfc5b8c0dcfb5ee0af5e9d729904c7eb971d9c1117f
[root@node1 ~]# docker run --name web2 -d --net bridge linux1874/myimg:v0.1
d39dea20d5ea0b52c42c67a8a9a36dcbc2ef78d654dfb9e1d88013306f2f5a50
[root@node1 ~]# docker ps
CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES
d39dea20d5ea linux1874/myimg:v0.1 "/bin/sh -c '/bin/ht…" 6 seconds ago Up 5 seconds web2
bced86e3dcb2 linux1874/myimg:v0.1 "/bin/sh -c '/bin/ht…" 11 seconds ago Up 11 seconds web1
[root@node1 ~]# docker container inspect myweb1 -f {{.NetworkSettings.Networks.bridge.NetworkID}}
Error: No such container: myweb1
[root@node1 ~]# docker container inspect web1 -f {{.NetworkSettings.Networks.bridge.NetworkID}}
2ae9aa6566561e8f1f5c98f4877b34b29a14ed8dd645933926b0615e9e0b2567
[root@node1 ~]# docker container inspect web2 -f {{.NetworkSettings.Networks.bridge.NetworkID}}
2ae9aa6566561e8f1f5c98f4877b34b29a14ed8dd645933926b0615e9e0b2567
[root@node1 ~]# docker network ls
NETWORK ID NAME DRIVER SCOPE
2ae9aa656656 bridge bridge local
93347fb33d89 host host local
a99b876eee4d none null local
[root@node1 ~]# docker container exec web1 ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue qlen 1
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
10: eth0@if11: <BROADCAST,MULTICAST,UP,LOWER_UP,M-DOWN> mtu 1500 qdisc noqueue
link/ether 02:42:ac:11:00:02 brd ff:ff:ff:ff:ff:ff
inet 172.17.0.2/16 brd 172.17.255.255 scope global eth0
valid_lft forever preferred_lft forever
[root@node1 ~]# docker container exec web2 ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue qlen 1
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
12: eth0@if13: <BROADCAST,MULTICAST,UP,LOWER_UP,M-DOWN> mtu 1500 qdisc noqueue
link/ether 02:42:ac:11:00:03 brd ff:ff:ff:ff:ff:ff
inet 172.17.0.3/16 brd 172.17.255.255 scope global eth0
valid_lft forever preferred_lft forever
[root@node1 ~]# docker container exec web2 wget -O - -q 172.17.0.2
this test file
[root@node1 ~]# docker container exec web1 wget -O - -q 172.17.0.3
this test file
提示:橋接式網路的容器間是可以通過docker0橋來通信;我們可以理解為同一橋上的網路為一個網路,他們的網路ID都是相同;上面兩個容器的網路ID都是bridge的ID;
示例:none網路容器的創建
[root@node1 ~]# docker ps
CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES
d39dea20d5ea linux1874/myimg:v0.1 "/bin/sh -c '/bin/ht…" 8 minutes ago Up 8 minutes web2
bced86e3dcb2 linux1874/myimg:v0.1 "/bin/sh -c '/bin/ht…" 9 minutes ago Up 9 minutes web1
[root@node1 ~]# docker run --name web3 -d --net none linux1874/myimg:v0.1
a0039645d551ef7089d7ff0e588864da48c68a0b301e28728e48d0b520a006ba
[root@node1 ~]# docker container inspect web3 -f {{.NetworkSettings.Networks.none.NetworkID}}
a99b876eee4d028f6d6410749ac863915711482e6f55aaf38071aabaae53ee2e
[root@node1 ~]# docker network ls
NETWORK ID NAME DRIVER SCOPE
2ae9aa656656 bridge bridge local
93347fb33d89 host host local
a99b876eee4d none null local
[root@node1 ~]# docker container exec web3 ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue qlen 1
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
[root@node1 ~]#
提示:可以看到none網路的容器網路ID是none的網路ID相同,內部也只有一個lo介面;
示例:共用式網路容器的創建
[root@node1 ~]# docker ps
CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES
a0039645d551 linux1874/myimg:v0.1 "/bin/sh -c '/bin/ht…" 2 minutes ago Up 2 minutes web3
d39dea20d5ea linux1874/myimg:v0.1 "/bin/sh -c '/bin/ht…" 12 minutes ago Up 12 minutes web2
bced86e3dcb2 linux1874/myimg:v0.1 "/bin/sh -c '/bin/ht…" 12 minutes ago Up 12 minutes web1
[root@node1 ~]# docker run --name web4 -d --net host linux1874/myimg:v0.1
f2dc3d0bb6992b6f0f93b3db50d952574c45473911a7133b735ae1b633855962
[root@node1 ~]# docker container inspect web4 -f {{.NetworkSettings.Networks.host.NetworkID}}
93347fb33d89a5abd7781ab1a01b51ad46dde4b2409b88d3d5f2e4a7bd0aed2e
[root@node1 ~]# docker network ls
NETWORK ID NAME DRIVER SCOPE
2ae9aa656656 bridge bridge local
93347fb33d89 host host local
a99b876eee4d none null local
[root@node1 ~]# docker container exec ip a
Error: No such container: ip
[root@node1 ~]# docker container exec web4 ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue qlen 1
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: ens33: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast qlen 1000
link/ether 00:0c:29:2e:06:0b brd ff:ff:ff:ff:ff:ff
inet 192.168.0.31/24 brd 192.168.0.255 scope global ens33
valid_lft forever preferred_lft forever
inet6 fe80::20c:29ff:fe2e:60b/64 scope link
valid_lft forever preferred_lft forever
3: docker0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue
link/ether 02:42:63:bb:cd:b4 brd ff:ff:ff:ff:ff:ff
inet 172.17.0.1/16 brd 172.17.255.255 scope global docker0
valid_lft forever preferred_lft forever
inet6 fe80::42:63ff:febb:cdb4/64 scope link
valid_lft forever preferred_lft forever
11: vethffac5a0@if10: <BROADCAST,MULTICAST,UP,LOWER_UP,M-DOWN> mtu 1500 qdisc noqueue master docker0
link/ether 82:b0:23:49:92:de brd ff:ff:ff:ff:ff:ff
inet6 fe80::80b0:23ff:fe49:92de/64 scope link
valid_lft forever preferred_lft forever
13: veth9e7a8c4@if12: <BROADCAST,MULTICAST,UP,LOWER_UP,M-DOWN> mtu 1500 qdisc noqueue master docker0
link/ether a6:d3:a2:c9:9f:45 brd ff:ff:ff:ff:ff:ff
inet6 fe80::a4d3:a2ff:fec9:9f45/64 scope link
valid_lft forever preferred_lft forever
[root@node1 ~]# docker container exec web4 hostname
node1
[root@node1 ~]# hostname
node1
[root@node1 ~]#
提示:host網路是共用宿主機的網路名稱空間,所以我們在容器內部看到的網路介面同宿主機上的網路介面一樣;
示例:聯盟式網路容器創建
[root@node1 ~]# docker images
REPOSITORY TAG IMAGE ID CREATED SIZE
linux1874/myimg v0.1 e408b1c6e04f 29 hours ago 1.22MB
busybox latest 78096d0a5478 10 days ago 1.22MB
centos 7 b5b4d78bc90c 2 weeks ago 203MB
nginx stable-alpine ab94f84cc474 4 weeks ago 21.3MB
[root@node1 ~]# docker run --name b1 --net container:web4 -it busybox
/ # [root@node1 ~]# docker ps
CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES
2b7517adb2ad busybox "sh" 13 seconds ago Up 13 seconds b1
f2dc3d0bb699 linux1874/myimg:v0.1 "/bin/sh -c '/bin/ht…" 22 minutes ago Up 22 minutes web4
a0039645d551 linux1874/myimg:v0.1 "/bin/sh -c '/bin/ht…" 27 minutes ago Up 27 minutes web3
d39dea20d5ea linux1874/myimg:v0.1 "/bin/sh -c '/bin/ht…" 36 minutes ago Up 36 minutes web2
bced86e3dcb2 linux1874/myimg:v0.1 "/bin/sh -c '/bin/ht…" 36 minutes ago Up 36 minutes web1
[root@node1 ~]# docker container exec b1 ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue qlen 1
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: ens33: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast qlen 1000
link/ether 00:0c:29:2e:06:0b brd ff:ff:ff:ff:ff:ff
inet 192.168.0.31/24 brd 192.168.0.255 scope global ens33
valid_lft forever preferred_lft forever
inet6 fe80::20c:29ff:fe2e:60b/64 scope link
valid_lft forever preferred_lft forever
3: docker0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue
link/ether 02:42:63:bb:cd:b4 brd ff:ff:ff:ff:ff:ff
inet 172.17.0.1/16 brd 172.17.255.255 scope global docker0
valid_lft forever preferred_lft forever
inet6 fe80::42:63ff:febb:cdb4/64 scope link
valid_lft forever preferred_lft forever
11: vethffac5a0@if10: <BROADCAST,MULTICAST,UP,LOWER_UP,M-DOWN> mtu 1500 qdisc noqueue master docker0
link/ether 82:b0:23:49:92:de brd ff:ff:ff:ff:ff:ff
inet6 fe80::80b0:23ff:fe49:92de/64 scope link
valid_lft forever preferred_lft forever
13: veth9e7a8c4@if12: <BROADCAST,MULTICAST,UP,LOWER_UP,M-DOWN> mtu 1500 qdisc noqueue master docker0
link/ether a6:d3:a2:c9:9f:45 brd ff:ff:ff:ff:ff:ff
inet6 fe80::a4d3:a2ff:fec9:9f45/64 scope link
valid_lft forever preferred_lft forever
提示:運行bubybox容器要註意容器前臺跑什麼程式,如果前臺沒有跑程式,容器一啟動就會處於退出狀態;我上面是先互動式運行/bin/sh,然後在用ctrl+p鬆開,然後再按ctrl+q兩個組合鍵來剝離當前終端,使得b1容器運行起來;從上面的信息來看,我們把b1容器的網路加入到web4容器的網路,b1和web4就都處於同一網路名稱空間;web4是共用宿主機網路名稱空間,所以b1的網路里也是能夠看到宿主機上的網路介面的;
[root@node1 ~]# docker ps CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES 2b7517adb2ad busybox "sh" 15 minutes ago Up 15 minutes b1 f2dc3d0bb699 linux1874/myimg:v0.1 "/bin/sh -c '/bin/ht…" 38 minutes ago Up 38 minutes web4 a0039645d551 linux1874/myimg:v0.1 "/bin/sh -c '/bin/ht…" 42 minutes ago Up 42 minutes web3 d39dea20d5ea linux1874/myimg:v0.1 "/bin/sh -c '/bin/ht…" 52 minutes ago Up 52 minutes web2 bced86e3dcb2 linux1874/myimg:v0.1 "/bin/sh -c '/bin/ht…" 52 minutes ago Up 52 minutes web1 [root@node1 ~]# ss -tnl State Recv-Q Send-Q Local Address:Port Peer Address:Port LISTEN 0 128 *:22 *:* LISTEN 0 100 127.0.0.1:25 *:* LISTEN 0 9 :::80 :::* LISTEN 0 128 :::22 :::* LISTEN 0 100 ::1:25 :::* [root@node1 ~]# docker attach b1 / # netstat -tnl Active Internet connections (only servers) Proto Recv-Q Send-Q Local Address Foreign Address State tcp 0 0 0.0.0.0:22 0.0.0.0:* LISTEN tcp 0 0 127.0.0.1:25 0.0.0.0:* LISTEN tcp 0 0 :::80 :::* LISTEN tcp 0 0 :::22 :::* LISTEN tcp 0 0 ::1:25 :::* LISTEN / # read escape sequence [root@node1 ~]# docker container exec -it web4 /bin/sh / # netstat -ntl Active Internet connections (only servers) Proto Recv-Q Send-Q Local Address Foreign Address State tcp 0 0 0.0.0.0:22 0.0.0.0:* LISTEN tcp 0 0 127.0.0.1:25 0.0.0.0:* LISTEN tcp 0 0 :::80 :::* LISTEN tcp 0 0 :::22 :::* LISTEN tcp 0 0 ::1:25 :::* LISTEN / # exit [root@node1 ~]#
提示:b1和web4和宿主機都處於同一網路名稱空間,在web4上監聽的80,在宿主機和b1上是能夠看到的,同時宿主機上監聽的其他埠,在b1和web4上也能夠看到;進入剝離的終端容器,需要用docker attach 命令進入;這樣一來我們就可以通過訪問宿主機的80埠訪問到容器內部的服務;也可以通過訪問b1主機的lo介面訪問到web4上的服務
[root@node1 ~]# docker attach b1
/ # ps aux
PID USER TIME COMMAND
1 root 0:00 sh
14 root 0:00 ps aux
/ # wget -O - -q http://127.0.0.1
this test file
/ # read escape sequence
[root@node1 ~]#
提示:雖然通過lo介面可以訪問到web4上的服務,但他們的其他資源還是相互隔離的,只是網路名稱空間是共用的同一個;
除此以外,我們在運行容器時還可以通過docker run 的一些選項來註入一些信息到容器內部
示例:註入hostname到容器內部
[root@node1 ~]# docker run --name web01 -it --rm --net bridge --hostname www.ilinux.io linux1874/myimg:v0.1 /bin/sh / # hostname www.ilinux.io / # exit [root@node1 ~]#
提示:可以看到在容器內部主機名就是我們運行容器時給定的主機名;--rm表示退出容器時刪除容器;-d 和--rm不能同時使用,這兩個選項是相互排斥的;
示例:從外部指定hostname與主機地址解析列表
[root@node1 ~]# docker run --name web01 -it --rm --net bridge --hostname www.ilinux.io --add-host www.test.com:1.1.1.1 --add-host www.test2.com:2.2.2.2 linux1874/myimg:v0.1 /bin/sh / # cat /etc/hosts 127.0.0.1 localhost ::1 localhost ip6-localhost ip6-loopback fe00::0 ip6-localnet ff00::0 ip6-mcastprefix ff02::1 ip6-allnodes ff02::2 ip6-allrouters 1.1.1.1 www.test.com 2.2.2.2 www.test2.com 172.17.0.4 www.ilinux.io www / # exit [root@node1 ~]#
提示:--add-host選項可以重覆使用很多次;應用場景,如果多容器間通信需要用到解析主機名的方式,那麼我們就需要用到註入主機名到主機的解析;
示例:註入dns伺服器地址到容器
[root@node1 ~]# docker run --name web01 -it --rm --net bridge --hostname www.ilinux.io --add-host www.test.com:1.1.1.1 --add-host www.test2.com:2.2.2.2 --dns 3.3.3.3 --dns 4.4.4.4 linux1874/myimg:v0.1 /bin/sh / # cat /etc/resolv.conf nameserver 3.3.3.3 nameserver 4.4.4.4 / # exit [root@node1 ~]#
提示:--dns表示指定dns伺服器地址;該選項也可同時使用多次用來指定多個dns伺服器地址;
示例:註入dns search
[root@node1 ~]# docker run --name web01 -it --rm --net bridge --hostname www.ilinux.io --add-host www.test.com:1.1.1.1 --add-host www.test2.com:2.2.2.2 --dns 3.3.3.3 --dns 4.4.4.4 --dns-search test.com --dns-search test2.com linux1874/myimg:v0.1 /bin/sh / # cat /etc/resolv.conf search test.com test2.com nameserver 3.3.3.3 nameserver 4.4.4.4 / # exit [root@node1 ~]#
提示:--dns-search 選項表示指定dns search;該選項也可同時使用多次,用來指定多個dns search;
示例:註入ip地址為容器ip地址
[root@node1 ~]# docker run --name web01 -it --rm --net bridge --hostname www.ilinux.io --add-host www.test.com:1.1.1.1 --add-host www.test2.com:2.2.2.2 --dns 3.3.3.3 --dns 4.4.4.4 --dns-search test.com --dns-search test2.com --ip 172.17.0.20 linux1874/myimg:v0.1 /bin/sh
docker: Error response from daemon: user specified IP address is supported on user defined networks only.
[root@node1 ~]# docker network ls
NETWORK ID NAME DRIVER SCOPE
2ae9aa656656 bridge bridge local
93347fb33d89 host host local
a99b876eee4d none null local
[root@node1 ~]# docker network create --subnet 10.0.0.0/24 mynet
e80b4e4cc6e9f2c772797c27b0cd81b93cc874e0ffbc5cc2ea2d3a1d9d5530fb
[root@node1 ~]# docker network ls
NETWORK ID NAME DRIVER SCOPE
2ae9aa656656 bridge bridge local
93347fb33d89 host host local
e80b4e4cc6e9 mynet bridge local
a99b876eee4d none null local
[root@node1 ~]# docker run --name web01 -it --rm --net mynet --hostname www.ilinux.io --add-host www.test.com:1.1.1.1 --add-host www.test2.com:2.2.2.2 --dns 3.3.3.3 --dns 4.4.4.4 --dns-search test.com --dns-search test2.com --ip 10.0.0.200 linux1874/myimg:v0.1 /bin/sh
/ # ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue qlen 1
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
29: eth0@if30: <BROADCAST,MULTICAST,UP,LOWER_UP,M-DOWN> mtu 1500 qdisc noqueue
link/ether 02:42:0a:00:00:c8 brd ff:ff:ff:ff:ff:ff
inet 10.0.0.200/24 brd 10.0.0.255 scope global eth0
valid_lft forever preferred_lft forever
/ # exit
[root@node1 ~]#
提示:docker 預設情況是不支持啟動容器指定ip地址的,指定ip地址只允許在自定義網路上指定;所以要想給容器指定ip地址,首先要自己創建一個網路名稱空間;運行容器時通過--net或--network指定網路,然後在指定IP地址就沒有問題了;
示例:給容器連接多個網路
[root@node1 ~]# docker run --name web1 -it --rm --network bridge linux1874/myimg:v0.1 /bin/sh
/ # ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue qlen 1
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
52: eth0@if53: <BROADCAST,MULTICAST,UP,LOWER_UP,M-DOWN> mtu 1500 qdisc noqueue
link/ether 02:42:ac:11:00:02 brd ff:ff:ff:ff:ff:ff
inet 172.17.0.2/16 brd 172.17.255.255 scope global eth0
valid_lft forever preferred_lft forever
/ # [root@node1 ~]# docker network ls
NETWORK ID NAME DRIVER SCOPE
03e2689873d0 bridge bridge local
93347fb33d89 host host local
e80b4e4cc6e9 mynet bridge local
a99b876eee4d none null local
[root@node1 ~]# docker network connect mynet web1
[root@node1 ~]# docker attach web1
/ # ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue qlen 1
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
52: eth0@if53: <BROADCAST,MULTICAST,UP,LOWER_UP,M-DOWN> mtu 1500 qdisc noqueue
link/ether 02:42:ac:11:00:02 brd ff:ff:ff:ff:ff:ff
inet 172.17.0.2/16 brd 172.17.255.255 scope global eth0
valid_lft forever preferred_lft forever
54: eth1@if55: <BROADCAST,MULTICAST,UP,LOWER_UP,M-DOWN> mtu 1500 qdisc noqueue
link/ether 02:42:0a:00:00:02 brd ff:ff:ff:ff:ff:ff
inet 10.0.0.2/24 brd 10.0.0.255 scope global eth1
valid_lft forever preferred_lft forever
/ #
提示:docker nerwork connect 類似給容器添加一塊網路,然後將容器里的網卡連接至我們指定的網路;
埠暴露
通常情況下我們運行docker容器都是使用的bridge網路,只有特殊場景才會用到自定義網路和其他網路;使用bridge網路有一個問題就是容器里的服務怎麼讓外界的主機訪問到呢?首先要讓外部訪問到容器內部的網路,這一層是不太可能了,原因是docker0橋是一個nat橋,它只可讓內部容器訪問外部主機,不可用外部主機訪問內部容器;如果要訪問,我們需要修改iptables的規則,很麻煩;除此之外還可以在宿主機上搭建一個反向代理,外部通過訪問代理,然後代理訪問容器內部服務,這樣的方式可行,但通常不這麼做;除此之外就只有把容器里跑的服務埠映射到宿主機上某埠,外部通過訪問宿主機的某埠,通過iptables規則做DNAT;通過埠映射到方式讓外部主機可以訪問到容器內部的服務;其實docker container run這個命令有一個-p的選項就是用來做這個事的;我們用-p選項來指定把宿主機的那個ip或埠映射到容器的某個ip或埠上;它的原理就是通過修改宿主機的iptables規則,做DNAT實現的;
示例:將容器80埠映射至宿主機某動態埠
[root@node1 ~]# docker run --name web01 -d -p 80 linux1874/myimg:v0.1
7dd827a920f07badc79911120aa9fee5dc74d8d9959f554ac9c19d911befd31c
[root@node1 ~]# docker container port web01
80/tcp -> 0.0.0.0:32768
[root@node1 ~]# iptables -t nat -nvL
Chain PREROUTING (policy ACCEPT 0 packets, 0 bytes)
pkts bytes target prot opt in out source destination
11 852 DOCKER all -- * * 0.0.0.0/0 0.0.0.0/0 ADDRTYPE match dst-type LOCAL
Chain INPUT (policy ACCEPT 0 packets, 0 bytes)
pkts bytes target prot opt in out source destination
Chain OUTPUT (policy ACCEPT 1 packets, 76 bytes)
pkts bytes target prot opt in out source destination
0 0 DOCKER all -- * * 0.0.0.0/0 !127.0.0.0/8 ADDRTYPE match dst-type LOCAL
Chain POSTROUTING (policy ACCEPT 1 packets, 76 bytes)
pkts bytes target prot opt in out source destination
0 0 MASQUERADE all -- * !br-e80b4e4cc6e9 10.0.0.0/24 0.0.0.0/0
6 379 MASQUERADE all -- * !docker0 172.17.0.0/16 0.0.0.0/0
0 0 MASQUERADE tcp -- * * 172.17.0.4 172.17.0.4 tcp dpt:80
Chain DOCKER (2 references)
pkts bytes target prot opt in out source destination
0 0 RETURN all -- br-e80b4e4cc6e9 * 0.0.0.0/0 0.0.0.0/0
0 0 RETURN all -- docker0 * 0.0.0.0/0 0.0.0.0/0
0 0 DNAT tcp -- !docker0 * 0.0.0.0/0 0.0.0.0/0 tcp dpt:32768 to:172.17.0.4:80
[root@node1 ~]#
提示:-p 指定容器里服務的埠,表示把容器的該埠映射到宿主機上的一個隨機埠,通常這個隨機埠是從32768開始;從上面的介面可以看到我們把80埠映射到宿主機上的32768埠上,隨之docker會在宿主機的iptables的nat表上添加一條DNAT規則;現在我們就可以通過訪問宿主機的32768埠來訪問容器內部的服務;通常我們不建議把容器里的服務隨機映射到宿主機上的一個埠;原因是客戶端不知道隨機埠後面的服務是什麼,當然訪問也就受限;
測試:訪問宿主機的32768埠看看是否能夠訪問到容器內部的web服務?
[root@docker_node1 ~]# ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN qlen 1
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: ens33: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP qlen 1000
link/ether 00:0c:29:22:36:7f brd ff:ff:ff:ff:ff:ff
inet 192.168.0.22/24 brd 192.168.0.255 scope global ens33
valid_lft forever preferred_lft forever
inet6 fe80::20c:29ff:fe22:367f/64 scope link
valid_lft forever preferred_lft forever
3: docker0: <NO-CARRIER,BROADCAST,MULTICAST,UP> mtu 1500 qdisc noqueue state DOWN
link/ether 02:42:72:cb:66:6d brd ff:ff:ff:ff:ff:ff
inet 172.17.0.1/16 brd 172.17.255.255 scope global docker0
valid_lft forever preferred_lft forever
[root@docker_node1 ~]# curl 192.168.0.31:32768
this test file
[root@docker_node1 ~]#
示例:將容器埠映射到指定主機埠
[root@node1 ~]# docker run --name web02 -d --net bridge -p 80:80 linux1874/myimg:v0.1
351ed7833aa1908c43abc061f5acdc7bd5e083ea097b26c1f4d4a7422bfbfcfa
[root@node1 ~]# docker container port web02
80/tcp -> 0.0.0.0:80
[root@node1 ~]# docker ps
CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES
351ed7833aa1 linux1874/myimg:v0.1 "/bin/sh -c '/bin/ht…" 23 seconds ago Up 21 seconds 0.0.0.0:80->80/tcp web02
7dd827a920f0 linux1874/myimg:v0.1 "/bin/sh -c '/bin/ht…" 10 minutes ago Up 10 minutes 0.0.0.0:32768->80/tcp web01
[root@node1 ~]# ss -tnl
State Recv-Q Send-Q Local Address:Port Peer Address:Port
LISTEN 0 128 *:22 *:*
LISTEN 0 100 127.0.0.1:25 *:*
LISTEN 0 128 :::80 :::*
LISTEN 0 128 :::22 :::*
LISTEN 0 100 ::1:25 :::*
LISTEN 0 128 :::32768 :::*
[root@node1 ~]# iptables -t nat -nvL
Chain PREROUTING (policy ACCEPT 2 packets, 466 bytes)
pkts bytes target prot opt in out source destination
12 912 DOCKER all -- * * 0.0.0.0/0 0.0.0.0/0 ADDRTYPE match dst-type LOCAL
Chain INPUT (policy ACCEPT 2 packets, 466 bytes)
pkts bytes target prot opt in out source destination
Chain OUTPUT (policy ACCEPT 1 packets, 76 bytes)
pkts bytes target prot opt in out source destination
0 0 DOCKER all -- * * 0.0.0.0/0 !127.0.0.0/8 ADDRTYPE match dst-type LOCAL
Chain POSTROUTING (policy ACCEPT 1 packets, 76 bytes)
pkts bytes target prot opt in out source destination
0 0 MASQUERADE all -- * !br-e80b4e4cc6e9 10.0.0.0/24 0.0.0.0/0
6 379 MASQUERADE all -- * !docker0 172.17.0.0/16 0.0.0.0/0
0 0 MASQUERADE tcp -- * * 172.17.0.4 172.17.0.4 tcp dpt:80
0 0 MASQUERADE tcp -- * * 172.17.0.2 172.17.0.2 tcp dpt:80
Chain DOCKER (2 references)
pkts bytes target prot opt in out source destination
0 0 RETURN all -- br-e80b4e4cc6e9 * 0.0.0.0/0 0.0.0.0/0
0 0 RETURN all -- docker0 * 0.0.0.0/0 0.0.0.0/0
1 60 DNAT tcp -- !docker0 * 0.0.0.0/0 0.0.0.0/0 tcp dpt:32768 to:172.17.0.4:80
0 0 DNAT tcp -- !docker0 * 0.0.0.0/0 0.0.0.0/0 tcp dpt:80 to:172.17.0.2:80
[root@node1 ~]#
提示:可以看到我們指定把容器的80埠映射到宿主機的80埠,宿主機上的80埠就處於監聽狀態了;同時iptables的nat表上又生成了一條新的DNT規則;
測試:通過其他主機訪問宿主機上的80看看是否能夠訪問到容器里的80服務?
[root@docker_node1 ~]# ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN qlen 1
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: ens33: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP qlen 1000
link/ether 00:0c:29:22:36:7f brd ff:ff:ff:ff:ff:ff
inet 192.168.0.22/24 brd 192.168.0.255 scope global ens33
valid_lft forever preferred_lft forever
inet6 fe80::20c:29ff:fe22:367f/64 scope link
valid_lft forever preferred_lft forever
3: docker0: <NO-CARRIER,BROADCAST,MULTICAST,UP> mtu 1500 qdisc noqueue state DOWN
link/ether 02:42:72:cb:66:6d brd ff:ff:ff:ff:ff:ff
inet 172.17.0.1/16 brd 172.17.255.255 scope global docker0
valid_lft forever preferred_lft forever
[root@docker_node1 ~]# curl 192.168.0.31
this test file
[root@docker_node1 ~]#
示例:將指定的容器埠映射到宿主機的指定ip上的動態埠
[root@node1 ~]# docker run --name web03 -d --net bridge -p 192.168.0.214::80 linux1874/myimg:v0.1
b4276ea0d0c0265a608b8111d64655a8667871f1b19cf971b42921a9a464c020
[root@node1 ~]# docker container port web03
80/tcp -> 192.168.0.214:32769
[root@node1 ~]# docker ps
CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES
b4276ea0d0c0 linux1874/myimg:v0.1 "/bin/sh -c '/bin/ht…" 15 seconds ago Up 15 seconds 192.168.0.214:32769->80/tcp web03
351ed7833aa1 linux1874/myimg:v0.1 "/bin/sh -c '/bin/ht…" 10 minutes ago Up 10 minutes 0.0.0.0:80->80/tcp web02
7dd827a920f0 linux1874/myimg:v0.1 "/bin/sh -c '/bin/ht…" 20 minutes ago Up 20 minutes 0.0.0.0:32768->80/tcp web01
[root@node1 ~]# ss -tnl
State Recv-Q Send-Q Local Address:Port Peer Address:Port
LISTEN 0 128 *:22 *:*
LISTEN 0 100 127.0.0.1:25 *:*
LISTEN 0 128 192.168.0.214:32769 *:*
LISTEN 0 128 :::80 :::*
LISTEN 0 128 :::22 :::*
LISTEN 0 100 ::1:25 :::*
LISTEN 0 128 :::32768 :::*
[root@node1 ~]# iptables -t nat -nvL
Chain PREROUTING (policy ACCEPT 0 packets, 0 bytes)
pkts bytes target prot opt in out source destination
15 1068 DOCKER all -- * * 0.0.0.0/0 0.0.0.0/0 ADDRTYPE match dst-type LOCAL
Chain INPUT (policy ACCEPT 0 packets, 0 bytes)
pkts bytes target prot opt in out source destination
Chain OUTPUT (policy ACCEPT 2 packets, 152 bytes)
pkts bytes target prot opt in out source destination
0 0 DOCKER all -- * * 0.0.0.0/0 !127.0.0.0/8 ADDRTYPE match dst-type LOCAL
Chain POSTROUTING (policy ACCEPT 2 packets, 152 bytes)
pkts bytes target prot opt in out source destination
0 0 MASQUERADE all -- * !br-e80b4e4cc6e9 10.0.0.0/24 0.0.0.0/0
6 379 MASQUERADE all -- * !docker0 172.17.0.0/16 0.0.0.0/0
0 0 MASQUERADE tcp -- * * 172.17.0.4 172.17.0.4 tcp dpt:80
0 0 MASQUERADE tcp -- * * 172.17.0.2 172.17.0.2 tcp dpt:80
0 0 MASQUERADE tcp -- * * 172.17.0.3 172.17.0.3 tcp dpt:80
Chain DOCKER (2 references)
pkts bytes target prot opt in out source destination
0 0 RETURN all -- br-e80b4e4cc6e9 * 0.0.0.0/0 0.0.0.0/0
0 0 RETURN all -- docker0 * 0.0.0.0/0 0.0.0.0/0
1 60 DNAT tcp -- !docker0 * 0.0.0.0/0 0.0.0.0/0 tcp dpt:32768 to:172.17.0.4:80
1 60 DNAT tcp -- !docker0 * 0.0.0.0/0 0.0.0.0/0 tcp dpt:80 to:172.17.0.2:80
0 0 DNAT tcp -- !docker0 * 0.0.0.0/0 192.168.0.214 tcp dpt:32769 to:172.17.0.3:80
[root@node1 ~]#
提示:可以看到宿主機上的192.168.0.214的32769處於監聽狀體;同時iptables的nat表示也新增了一條DNAT規則;
測試:通過其他主機訪問宿主機的192.168.0.214的32769埠,看看是否能夠訪問到容器內部的80服務?
[root@docker_node1 ~]# ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN qlen 1
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: ens33: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP qlen 1000
link/ether 00:0c:29:22:36:7f brd ff:ff:ff:ff:ff:ff
inet 192.168.0.22/24 brd 192.168.0.255 scope global ens33
valid_lft forever preferred_lft forever
inet6 fe80::20c:29ff:fe22:367f/64 scope link
valid_lft forever preferred_lft forever
3: docker0: <NO-CARRIER,BROADCAST,MULTICAST,UP> mtu 1500 qdisc noqueue state DOWN
link/ether 02:42:72:cb:66:6d brd ff:ff:ff:ff:ff:ff
inet 172.17.0.1/16 brd 172.17.255.255 scope global docker0
valid_lft forever preferred_lft forever
[root@docker_node1 ~]# curl 192.168.0.214:32769
this test file
[root@docker_node1 ~]#
示例:將容器的埠映射至宿主機的指定ip的指定埠
[root@node1 ~]# docker run --name web04 -d --net bridge -p 192.168.0.214:81:80 linux1874/myimg:v0.1
1f58cd21b2c861b8761032a07d9e47d3bf1a2c072816d931918171ea38a9c090
[root@node1 ~]# docker container port web04
80/tcp -> 192.168.0.214:81
[root@node1 ~]# docker ps
CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES
1f58cd21b2c8 linux1874/myimg:v0.1 "/bin/sh -c '/bin/ht…" 19 seconds ago Up 17 seconds 192.168.0.214:81->80/tcp web04
b4276ea0d0c0 linux1874/myimg:v0.1 "/bin/sh -c '/bin/ht…" 7 minutes ago Up 7 minutes 192.168.0.214:32769->80/tcp web03
351ed7833aa1 linux1874/myimg:v0.1 "/bin/sh -c '/bin/ht…" 17 minutes ago Up 17 minutes 0.0.0.0:80->80/tcp web02
7dd827a920f0 linux1874/myimg:v0.1 "/bin/sh -c '/bin/ht…" 27 minutes ago Up 27 minutes 0.0.0.0:32768->80/tcp web01
[root@node1 ~]# ss -tnl
State Recv-Q Send-Q Local Address:Port Peer Address:Port
LISTEN 0 128 192.168.0.214:81 *:*
LISTEN 0 128 *:22 *:*
LISTEN 0 100 127.0.0.1:25 *:*
LISTEN 0 128 192.168.0.214:32769 *:*
LISTEN 0 128 :::80 :::*
LISTEN 0 128 :::22 :::*
LISTEN 0 100 ::1:25 :::*
LISTEN 0 128 :::32768 :::*
[root@node1 ~]# iptables -t nat -nvL
Chain PREROUTING (policy ACCEPT 0 packets, 0 bytes)
pkts bytes target prot opt in out source destination
16 1128 DOCKER all -- * * 0.0.0.0/0 0.0.0.0/0 ADDRTYPE match dst-type LOCAL
Chain INPUT (policy ACCEPT 0 packets, 0 bytes)
pkts bytes target prot opt in out source destination
Chain OUTPUT (policy ACCEPT 1 packets, 76 bytes)
pkts bytes target prot opt in out source destination
0 0 DOCKER all -- * * 0.0.0.0/0 !127.0.0.0/8 ADDRTYPE match dst-type LOCAL
Chain POSTROUTING (policy ACCEPT 1 packets, 76 bytes)
pkts bytes target prot opt in out source destination
0 0 MASQUERADE all -- * !br-e80b4e4cc6e9 10.0.0.0/24 0.0.0.0/0
6 379 MASQUERADE all -- * !docker0 172.17.0.0/16 0.0.0.0/0
0 0 MASQUERADE tcp -- * * 172.17.0.4 172.17.0.4 tcp dpt:80
0 0 MASQUERADE tcp -- * * 172.17.0.2 172.17.0.2 tcp dpt:80
0 0 MASQUERADE tcp -- * * 172.17.0.3 172.17.0.3 tcp dpt:80
0 0 MASQUERADE tcp -- * * 172.17.0.5 172.17.0.5 tcp dpt:80
Chain DOCKER (2 references)
pkts bytes target prot opt in out source destination
0 0 RETURN all -- br-e80b4e4cc6e9 * 0.0.0.0/0 0.0.0.0/0
0 0 RETURN all -- docker0 * 0.0.0.0/0 0.0.0.0/0
1 60 DNAT tcp -- !docker0 * 0.0.0.0/0 0.0.0.0/0 tcp dpt:32768 to:172.17.0.4:80
1 60 DNAT tcp -- !docker0 * 0.0.0.0/0 0.0.0.0/0 tcp dpt:80 to:172.17.0.2:80
1 60 DNAT tcp -- !docker0 * 0.0.0.0/0 192.168.0.214 tcp dpt:32769 to:172.17.0.3:80
0 0 DNAT tcp -- !docker0 * 0.0.0.0/0 192.168.0.214 tcp dpt:81 to:172.17.0.5:80
[root@node1 ~]#
提示:可以看到宿主機上的81埠處於監聽狀態,同時iptables中的nat表也新加了一條DNAT規則;
測試:用其他主機訪問192.168.0.214的81埠看看是否能夠訪問到容器里80服務?
[root@docker_node1 ~]# ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN qlen 1
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: ens33: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP qlen 1000
link/ether 00:0c:29:22:36:7f brd ff:ff:ff:ff:ff:ff
inet 192.168.0.22/24 brd 192.168.0.255 scope global ens33
valid_lft forever preferred_lft forever
inet6 fe80::20c:29ff:fe22:367f/64 scope link
valid_lft forever preferred_lft forever
3: docker0: <NO-CARRIER,BROADCAST,MULTICAST,UP> mtu 1500 qdisc noqueue state DOWN
link/ether 02:42:72:cb:66:6d brd ff:ff:ff:ff:ff:ff
inet 172.17.0.1/16 brd 172.17.255.255 scope global docker0
valid_lft forever preferred_lft forever
[root@docker_node1 ~]# curl 192.168.0.214:81
this test file
[root@docker_node1 ~]#
示例:將容器多個埠映射到宿主機
[root@node1 ~]# docker run --name web05 -d --net bridge -p 80 -p 443 linux1874/myimg:v0.1
898e99cf0f37104954913488717969584d35677a0660874a52a502934599caf7
[root@node1 ~]# docker container port web05
443/tcp -> 0.0.0.0:32770
80/tcp -> 0.0.0.0:32771
[root@node1 ~]# ss -ntl
State Recv-Q Send-Q Local Address:Port Peer Address:Port
LISTEN 0 128 192.168.0.214:81 *:*
LISTEN 0 128 *:22 *:*
LISTEN 0 100 127.0.0.1:25 *:*
LISTEN 0 128 192.168.0.214:32769 *:*
LISTEN 0 128 :::80 :::*
LISTEN 0 128 :::22 :::*
LISTEN 0 100 ::1:25 :::*
LISTEN 0 128 :::32768 :::*
LISTEN 0 128 :::32770 :::*
LISTEN 0 128 :::32771 :::*
[root@node1 ~]# docker ps
CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES
898e99cf0f37 linux1874/myimg:v0.1 "/bin/sh -c '/bin/ht…" 31 seconds ago Up 29 seconds 0.0.0.0:32771->80/tcp, 0.0.0.0:32770->443/tcp web05
1f58cd21b2c8 linux1874/myimg:v0.1 "/bin/sh -c '/bin/ht…" 19 minutes ago Up 19 minutes 192.168.0.214:81->80/tcp web04
b4276ea0d0c0 linux1874/myimg:v0.1 "/bin/sh -c '/bin/ht…" 26 minutes ago Up 26 minutes 192.168.0.214:32769->80/tcp web03
351ed7833aa1 linux1874/myimg:v0.1 "/bin/sh -c '/bin/ht…" 35 minutes ago Up 35 minutes 0.0.0.0:80->80/tcp web02
7dd827a920f0 linux1874/myimg:v0.1 "/bin/sh -c '/bin/ht…" 46 minutes ago Up 46 minutes 0.0.0.0:32768->80/tcp web01
[root@node1 ~]# iptables -t nat -nvL
Chain PREROUTING (policy ACCEPT 0 packets, 0 bytes)
pkts bytes target prot opt in out source destination
17 1188 DOCKER all -- * * 0.0.0.0/0 0.0.0.0/0 ADDRTYPE match dst-type LOCAL
Chain INPUT (policy ACCEPT 0 packets, 0 bytes)
pkts bytes target prot opt in out source destination
Chain OUTPUT (policy ACCEPT 3 packets, 228 bytes)
pkts bytes target prot opt in out source destination
0 0 DOCKER all -- * * 0.0.0.0/0 !127.0.0.0/8 ADDRTYPE match dst-type LOCAL
Chain POSTROUTING (policy ACCEPT 3 packets, 228 bytes)
pkts bytes target prot opt in out source destination
0 0 MASQUERADE all -- * !br-e80b4e4cc6e9 10.0.0.0/24 0.0.0.0/0
6 379 MASQUERADE all -- * !docker0 172.17.0.0/16 0.0.0.0/0
0 0 MASQUERADE tcp -- * * 172.17.0.4 172.17.0.4 tcp dpt:80
0 0 MASQUERADE tcp -- * * 172.17.0.2 172.17.0.2 tcp dpt:80
0 0 MASQUERADE tcp -- * * 172.17.0.3 172.17.0.3 tcp dpt:80
0 0 MASQUERADE tcp -- * * 172.17.0.5 172.17.0.5 tcp dpt:80
0 0 MASQUERADE tcp -- * * 172.17.0.6 172.17.0.6 tcp dpt:443
0 0 MASQUERADE tcp -- * * 172.17.0.6 172.17.0.6 tcp dpt:80
Chain DOCKER (2 references)
pkts bytes target prot opt in out source destination
0 0 RETURN all -- br-e80b4e4cc6e9 * 0.0.0.0/0 0.0.0.0/0
0 0 RETURN all -- docker0 * 0.0.0.0/0 0.0.0.0/0
1 60 DNAT tcp -- !docker0 * 0.0.0.0/0 0.0.0.0/0 tcp dpt:32768 to:172.17.0.4:80
1 60 DNAT tcp -- !docker0 * 0.0.0.0/0 0.0.0.0/0 tcp dpt:80 to:172.17.0.2:80
1 60 DNAT tcp -- !docker0 * 0.0.0.0/0 192.168.0.214 tcp dpt:32769 to:172.17.0.3:80
1 60 DNAT tcp -- !docker0 * 0.0.0.0/0 192.168.0.214 tcp dpt:81 to:172.17.0.5:80
0 0 DNAT tcp -- !docker0 * 0.0.0.0/0 0.0.0.0/0 tcp dpt:32770 to:172.17.0.6:443
0 0 DNAT tcp -- !docker0 * 0.0.0.0/0 0.0.0.0/0 tcp dpt:32771 to:172.17.0.6:80
[root@node1 ~]#
提示:-p選項可以使用多次,來指定需要映射埠和宿主機的埠映射關係;除此還可以使用-P(大寫) 加--expose來指定要映射的埠
[root@node1 ~]# docker run --name web06 -d --net bridge -P --expose 80 --expose 443 linux1874/myimg:v0.1
b377f6d380828ece81d69fd83cf7678800466f45689850a7e47dde1619602ffa
[root@node1 ~]# docker container port web06
443/tcp -> 0.0.0.0:32772
80/tcp -> 0.0.0.0:32773
[root@node1 ~]# docker ps
CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES
b377f6d38082 linux1874/myimg:v0.1 "/bin/sh -c '/bin/ht…" 19 seconds ago Up 18 seconds 0.0.0.0:32773->80/tcp, 0.0.0.0:32772->443/tcp web06
898e99cf0f37 linux1874/myimg:v0.1 "/bin/sh -c '/bin/ht…" 3 minutes ago Up 3 minutes 0.0.0.0:32771->80/tcp, 0.0.0.0:32770->443/tcp web05
1f58cd21b2c8 linux1874/myimg:v0.1 "/bin/sh -c '/bin/ht…" 22 minutes ago Up 22 minutes 192.168.0.214:81->80/tcp web04
b4276ea0d0c0 linux1874/myimg:v0.1 "/bin/sh -c '/bin/ht…" 29 minutes ago Up 29 minutes 192.168.0.214:32769->80/tcp web03
351ed7833aa1 linux1874/myimg:v0.1 "/bin/sh -c '/bin/ht…" 39 minutes ago Up 39 minutes 0.0.0.0:80->80/tcp web02
7dd827a920f0 linux1874/myimg:v0.1 "/bin/sh -c '/bin/ht…" 49 minutes ago Up 49 minutes 0.0.0.0:32768->80/tcp web01
[root@node1 ~]# ss -tnl
State Recv-Q Send-Q Local Address:Port Peer Address:Port
LISTEN 0 128 192.168.0.214:81 *:*
LISTEN 0 128 *:22 *:*
LISTEN 0 100 127.0.0.1:25 *:*
LISTEN 0 128 192.168.0.214:32769 *:*
LISTEN 0 128 :::80 :::*
LISTEN 0 128 :::22 :::*
LISTEN 0 100 ::1:25 :::*
LISTEN 0 128 :::32768 :::*
LISTEN 0 128 :::32770 :::*
LISTEN 0 128 :::32771 :::*
LISTEN 0 128 :::32772 :::*
LISTEN 0 128 :::32773 :::*
[root@node1 ~]# iptables -t nat -nvL
Chain PREROUTING (policy ACCEPT 0 packets, 0 bytes)
pkts bytes target prot opt in out source destination
17 1188 DOCKER all -- * * 0.0.0.0/0 0.0.0.0/0 ADDRTYPE match dst-type LOCAL
Chain INPUT (policy ACCEPT 0 packets, 0 bytes)
pkts bytes target prot opt in out source destination
Chain OUTPUT (policy ACCEPT 3 packets, 228 bytes)
pkts bytes target prot opt in out source destination
0 0 DOCKER all -- * * 0.0.0.0/0 !127.0.0.0/8 ADDRTYPE match dst-type LOCAL
Chain POSTROUTING (policy ACCEPT 3 packets, 228 bytes)
pkts bytes target prot opt in out source destination
0 0 MASQUERADE all -- * !br-e80b4e4cc6e9 10.0.0.0/24 0.0.0.0/0
6 379 MASQUERADE all -- * !docker0 172.17.0.0/16 0.0.0.0/0
0 0 MASQUERADE tcp -- * * 172.17.0.4 172.17.0.4 tcp dpt:80
0 0 MASQUERADE tcp -- * * 172.17.0.2 172.17.0.2 tcp dpt:80
0 0 MASQUERADE tcp -- * * 172.17.0.3 172.17.0.3 tcp dpt:80
0 0 MASQUERADE tcp -- * * 172.17.0.5 172.17.0.5 tcp dpt:80
0 0 MASQUERADE tcp -- * * 172.17.0.6 172.17.0.6 tcp dpt:443
0 0 MASQUERADE tcp -- * * 172.17.0.6 172.17.0.6 tcp dpt:80
0 0 MASQUERADE tcp -- * * 172.17.0.7 172.17.0.7 tcp dpt:443
0 0 MASQUERADE tcp -- * * 172.17.0.7 172.17.0.7 tcp dpt:80
Chain DOCKER (2 references)
pkts bytes target prot opt in out source destination
0 0 RETURN all -- br-e80b4e4cc6e9 * 0.0.0.0/0 0.0.0.0/0
0 0 RETURN all -- docker0 * 0.0.0.0/0 0.0.0.0/0
1 60 DNAT tcp -- !docker0 * 0.0.0.0/0 0.0.0.0/0 tcp dpt:32768 to:172.17.0.4:80
1 60 DNAT tcp -- !docker0 * 0.0.0.0/0 0.0.0.0/0 tcp dpt:80 to:172.17.0.2:80
1 60 DNAT tcp -- !docker0 * 0.0.0.0/0 192.168.0.214 tcp dpt:32769 to:172.17.0.3:80
1 60 DNAT tcp -- !docker0 * 0.0.0.0/0 192.168.0.214 tcp dpt:81 to:172.17.0.5:80
0 0 DNAT tcp -- !docker0 * 0.0.0.0/0 0.0.0.0/0 tcp dpt:32770 to:172.17.0.6:443
0 0 DNAT tcp -- !docker0 * 0.0.0.0/0 0.0.0.0/0 tcp dpt:32771 to:172.17.0.6:80
0 0 DNAT tcp -- !docker0 * 0.0.0.0/0 0.0.0.0/0 tcp dpt:32772 to:172.17.0.7:443
0 0 DNAT tcp -- !docker0 * 0.0.0.0/0 0.0.0.0/0 tcp dpt:32773 to:172.17.0.7:80
[root@node1 ~]#
提示:使用-P(大寫) --expose 的方式暴露埠,不可以選擇暴露給宿主機的某個ip的某個埠或隨機埠,只能暴露給宿主機的所有ip的隨機埠;簡單說就是不能指定固定宿主機的IP和埠;
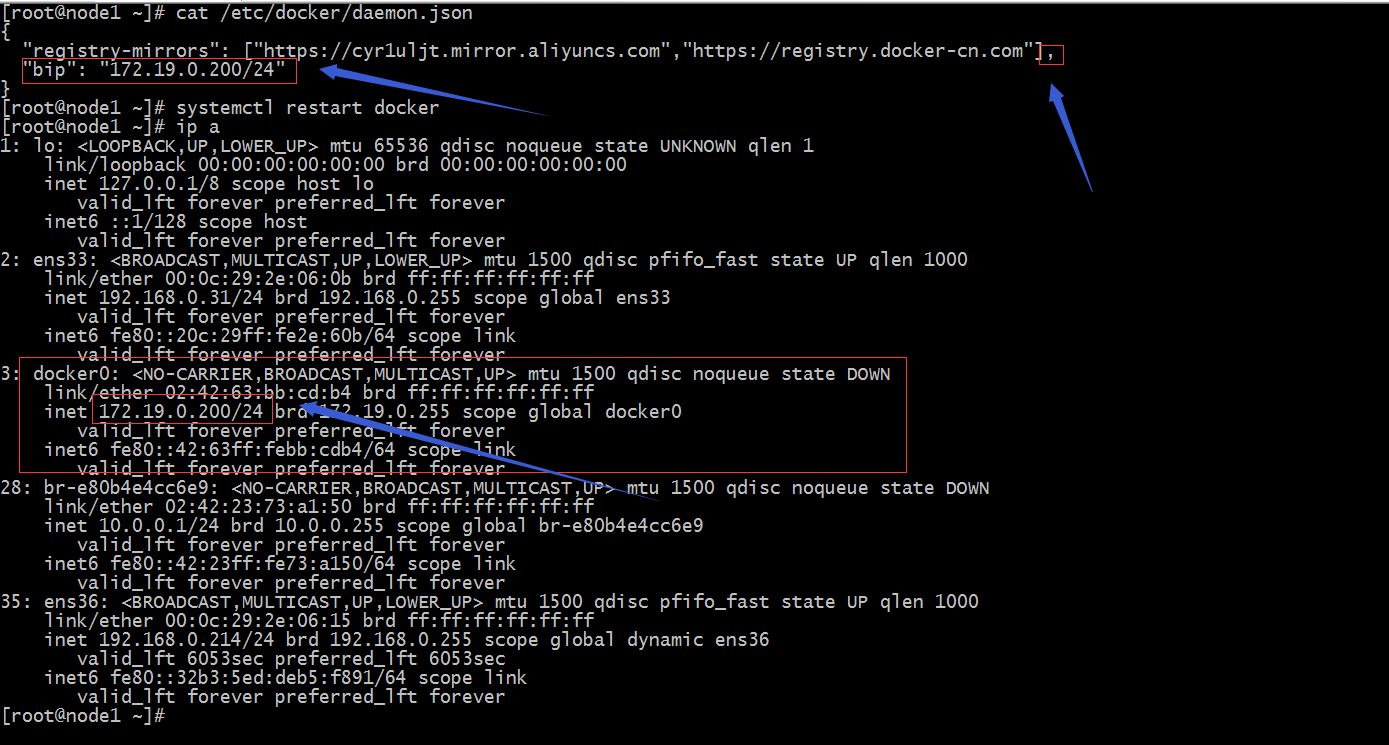
示例:修改docker0橋的網路屬性
提示:修改docker0橋的網路信息,我們需要在/etc/docker/daemon.json這個文件中添加一項bip來指定docker0橋的網路地址;這裡需要註意一點的是如果這個文件沒有內容我們直接用大括弧加“bip”: "ip地址和子網掩碼"即可,如果有其他項需要註意後面的逗號,如上所示;如果後續還有其他配置,需要在最後的一項後面加逗號,然後在添加其他配置;末尾可以不寫逗號;其實這個文件中可以添加很多配置,對於配置docker0橋的屬性也有很多,但核心配置選項就是bip,它主要是用來指定docker0橋的ip地址和子網掩碼信息;其他的選項可以不用指定,它們都可以通過bip這個選項自動計算生成;有關/etc/docker/daemon.json文件的相關說明可以參考官方文檔https://docs.docker.com/engine/reference/commandline/dockerd/#run-multiple-daemons;


